Blog
pfSense Rules not Working?

[adinserter name=”TopOfPost”]pfSense has to be the greatest thing to ever happen to the open source firewall movement. It’s a one of those open source products that’s truly a game changer. It runs on just about any hardware, whether it be a PC or an old XBOX. Companies have even built custom designed hardware around pfSense with multiple network ports and hardware acceleration.
What makes pfSense so great is that is the combination of three things: 1) awesome hardware support, 2) a fantastic easy to use user interface (UI), and 3) its rock solid reliability.
But with most open source projects, even one with some commercial backing, pfSense struggles in the area of support and support documentation. Such is the case with this post. You’re probably here because some pfSesnse rules not working in your environment. You’ve applied them you’ve tested them, and low and behold some device that should not have access to some other device or network still has access! It can be very frustrating! The good news, is the fixes are pretty simple.
pfSense Rules Not Working
The first thing you need to do is understand how pfSense rules work. They took a slightly different path than some firewall software or router access lists work. It actually makes things simpler, but if you don’t understand the basics it can be a real pain!
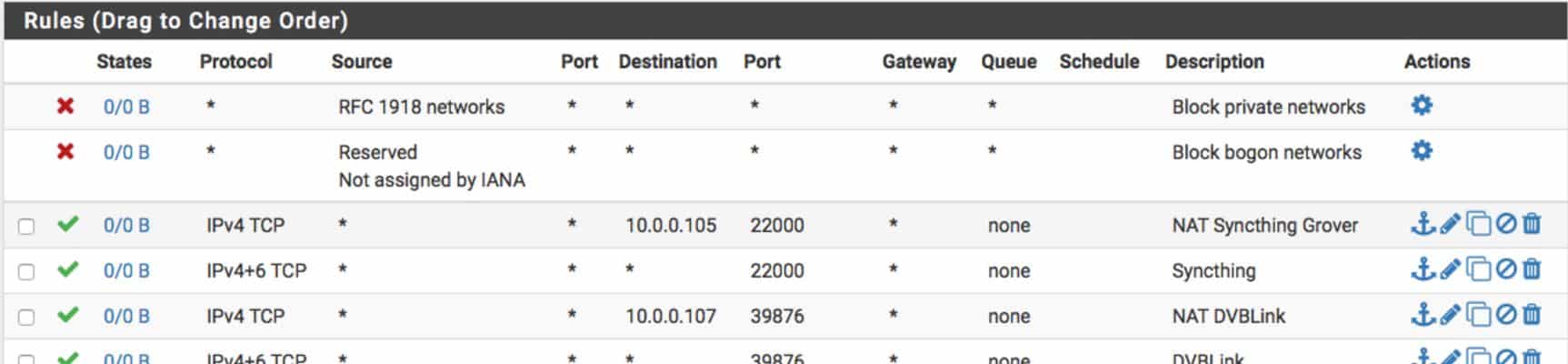
pfSense Processes Rules from Top to Bottom
As simple as this sounds, you’d be surprised how often this turns out to be the problem with a pfSense rule not working! The very first thing to know is that pfSense processes rules from the top of the screen to the bottom of the screen. If you have a pass all rule at the top, then all blocks/rejects below that rule will be ignored. Same thing goes for a block all at the top of the list, any pass rules that follow would be ignored. So make sure that your rules are in the right order.
pfSense Rule Adds/Changes do NOT Effect Existing Sessions
This one gets lots of people. pfSense rules do not effect this existing state table. So for example, if you have aping in progress, or a telnet session open to a server and you create a pfSense rule to block that access nothing happens. The connection still works. Pings will keep pinging, and the telnet session will stay open (or whatever service was connected, like HTTP, FTP, etc).
To kill existing sessions, you’ll need to go Diagnostics –> States and kill the existing sessions. Once they are killed, the pfSense rule you create will block an new sessions from being established.
pfSense Only Processes Rules on Ingress to a Port
Unlike many firewalls pfSense only processes rules on the ingress of a port. If pfSense rules not working in the way you expected, make sure it is applied on the ingress to a port on the firewall. If it is applied to the egress it will not function correctly.
I hope this helps you solve the reason that your pfSense rules are not working! If you’re looking for an awesome pfSense firewall to use on your home network, I highly recommend this one from Amazon. I and several of my friends have it!






OH MY LORD. I’ve been fighting this problem for days! I had no idea that pfSense rule changes did not clear the state table! This explains why rebooting the router sometimes “fixed” my problem! Thank you so much for this! LIFE SAVER!
I was having the same problem!
Many thanks for this post.
You saved mi life!
4.5
I’ve set up block rules for the LAN side, made sure that they were above the allow rules, set them to block on a schedule, and they worked. However the states weren’t clearing. Only newly generated traffic would be blocked.
However like you said, the states are not supposed to reset when a schedule is turned ON, but they are supposed to reset when a schedule is turned OFF. This seems to follow the logic in the NetGate documentation, and there’s an option under System/Advanced/Miscelaneous. It says “(Checkbox) Do not kill connections when schedule expires
By default, when a schedule expires, connections permitted by that schedule are killed. This option overrides that behavior by not clearing states for existing connections. to NOT reset states when schedules go inactive.”
I’ve rebooted the machine to test it, and it didn’t seem to make a difference. It was sad because it was up for 326 days before I rebooted it.
I think scheduling firewall rules is very sketchy. There’s a few different sites I’ve found that went over some of the issues that people were having. One said that the state reset feature only works if you use the times in the dropdowns 0-15-30-45… they made mention of a built-in cron job that runs every 15 minutes for state clearing.
I’m testing this tomorrow. I love pfSense but I think that this feature is not something that they really put too much thought in, because outside of a home situation, I couldn’t see people using it much.
When is a firewall rule not a rule? When it’s on a schedule, then it’s mostly a rule… LOL