Blog
Use Airport Extreme Guest Network in Bridge Mode

[adinserter name=”TopOfPost”]Is it possible to use Apple’s Airport Extreme Guest Network without using the Airport as your main router? YES. This is one of those situations where Apple really pisses me off. Apple loves to make their technologies proprietary and compatible with only other Apple gear. And that really sucks when you need their gear to work with other manufactures products out of necessity and Apple we’re talking about things that have been industry standards for decades!
The Airport Extreme Guest Wireless network can be used with almost any other brand of router as your main router, as long is it supports VLANs, but Apple has gone out of there way to make sure you don’t know that. The Apple overlords have gone too far in this case, and I am going to show you how it really works!
Using The Airport Extreme Guest Network with a Third Party Router
 I bought several Airport Extremes when we built our new home in 2015. I’ve always liked that the Airports just work, and always reliably. Something Apple has generally been known for. So I wanted to stick with them in my new house. One of the features I was excited about was the Airport Extreme Guest Network. This feature allows you to create a second SSID, very simply that has access only to the internet. Generally your normal SSID-Guest. This network is firewalled off from your home network, allowing guests to surf the web without getting access to your private data.
I bought several Airport Extremes when we built our new home in 2015. I’ve always liked that the Airports just work, and always reliably. Something Apple has generally been known for. So I wanted to stick with them in my new house. One of the features I was excited about was the Airport Extreme Guest Network. This feature allows you to create a second SSID, very simply that has access only to the internet. Generally your normal SSID-Guest. This network is firewalled off from your home network, allowing guests to surf the web without getting access to your private data.
However, Apple did something only Apple does. They made the requirement that the main router that connects your home to the Internet also be an Airport Extreme, otherwise the Guest Network simply does not work. So for the last year I’ve been without a guest network, a feature that I really wanted because I refuse to use the Airport as my main router. Honestly, I can’t. My network is too complex, and even if it wasn’t I have FiOS Internet which means I would have to call and get my ONT re-provisioned to use the Ethernet jack instead of MoCA (coax) which would be a major hassle.
Investigating Apple’s Guest Network
 So this morning I decided to do a little tinkering. I plugged the Airport directly into my laptop with Wireshark installed and while watching the traffic I turned on the Guest Network feature. Something I saw was very interesting. There were frames crossing the network with 802.1q tags on them. That’s right! The guest network was just using a separate VLAN to operate. In fact, it was VLAN 1003. This of course got my gears turning.
So this morning I decided to do a little tinkering. I plugged the Airport directly into my laptop with Wireshark installed and while watching the traffic I turned on the Guest Network feature. Something I saw was very interesting. There were frames crossing the network with 802.1q tags on them. That’s right! The guest network was just using a separate VLAN to operate. In fact, it was VLAN 1003. This of course got my gears turning.
All of my Airport Extremes plug into a Netgear ProSafe switch. My ActionTech MI424WR is also plugged into this same switch. The question buzzing through my brain was “Is this really that simple? If enable VLAN tagging on those ports and turn on a VLAN interface on the MI424WR will it work?” Of course I had to find out!
Enable the Airport Extreme Guest Network
The first thing you need to do is enable the Guest Network on the Airport Extreme. Open the Airport Utility under Finder–>Go–>Utilities–>Airport Utility and then select the name of your Airport Extreme base station. On the pop-up click edit and enter the devices password. Click on the wireless tab. At the bottom tick the box that says “Enable Guest Network” and enter the name you want to call the network. Again, most people use their normal SSID and add “-Guest” to it. Generally you’ll set the “Guest Network Security” to “None”. Otherwise you’ll still have to give all of your guests a password, which might be useful for some people. In my case I left it wide open.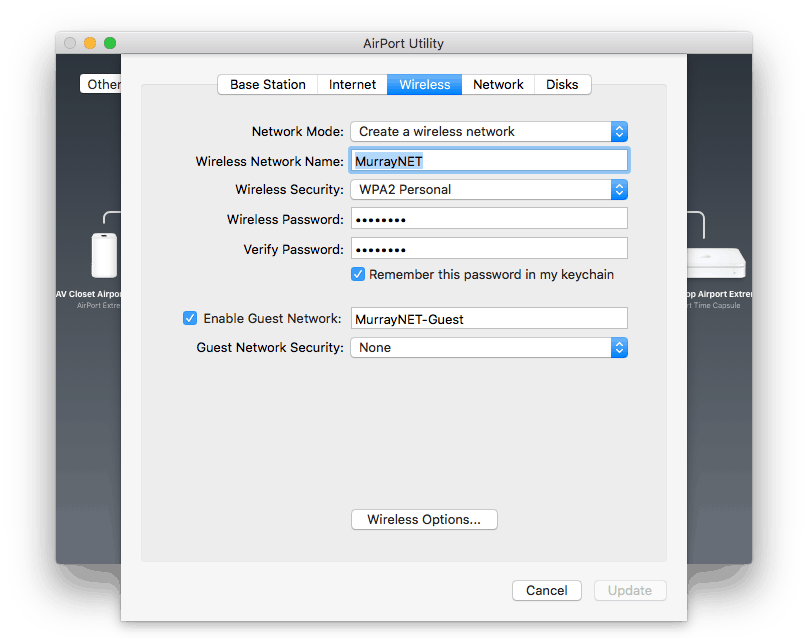
Enable VLAN 1003 on your Switch
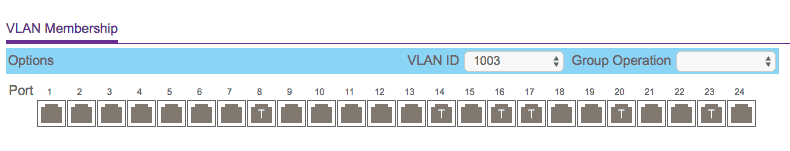
If you’re Airport Extreme is not connected directly to your router, you’ll need to enable VLAN tagging on the the ports of your switch in order for it to pass the VLAN 1003 802.1q tags to your router. If your Airport is connected directly, just go on to the next step.
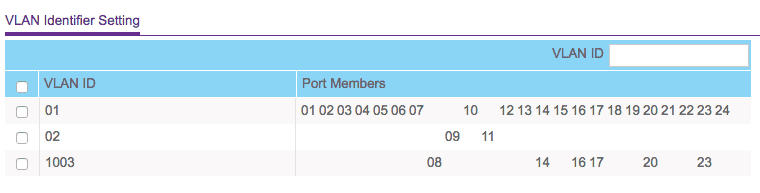
If this is your first new VLAN on your switch, you’ll want to make sure all of your existing ports are set to PVID 1. This means they’ll just act as part of your normal network. They’ll pass traffic normally. Then created a new VLAN ID of 1003. This alone does nothing, but lets the switch know we want to use this ID somewhere on our network.
To make the magic happen select that VLAN and then select all of the ports that have an Airport Extreme plugged into them, and the port plugged into your router. In my case I dedicated a second port on my router for this VLAN, but that’s not necessary.
You’ll wind up with a VLAN configuration that looks something like the picture below. Ignore VLAN 2, this is unique to my network, and you won’t have it. You’ll see that port 14 is untagged on VLAN 1 which is the normal network, and tagged on VLAN 1003, allowing it to also pass traffic for that network if it receives an 802.1q tag for that ID.
Configure your Router to Imitate the Airport Extreme Guest Network
At this point traffic should be passing all the way to your router, but your router doesn’t know what to do with it, and since there is no DHCP server on this VLAN, connected devices cannot get an IP address.
This is going to be very specific to your type of router, and not all routers support VLANs. This example is from my ActionTech. A Linksys, NetGear, pfSense, SonicWall, or others should all support VLANs.
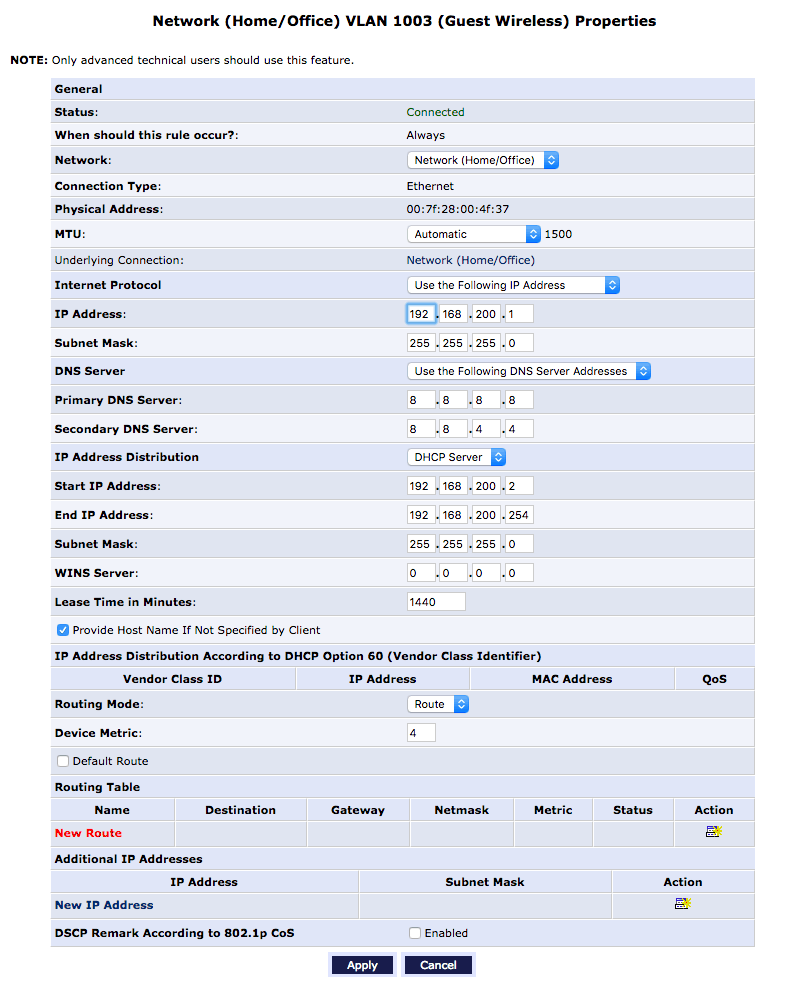
Create a new VLAN on the ActionTech MI424WR under My Network–>Connections–>Add. This will be a tagged network. Name it Home/Office Guest Wireless (VLAN 1003) and enter 1003 as the VLAN ID and the click Apply. Edit the new network connection and change Internet Protocol to “Use the Following IP Address” and pick a subnet that suites your fancy. I decided to go with 192.168.200.0/24. Enter the names of the DNS servers you use, I prefer Google DNS, especially for guest networks. Lastly, under IP Address distribution, enable the DHCP server and select a range of IPs for it to give out. I just gave it everything but .1 since nothing else should ever be on this network.
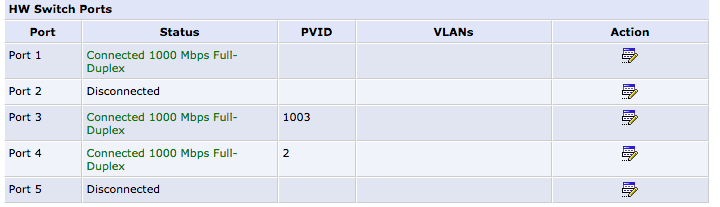
In my case I wanted to dedicate port 3 for this VLAN because I plan to rate limit this network to 15 Mb/s to keep people from using all of my bandwidth. Under My Network–>Connections–>Ethernet/Coaxial click settings and click the Hardware Switch Ports. I assigned Port 3 to be dedicated to VLAN 1003. After that I plugged another cable from the MI424WR’s port 3 into port 8 of my NetGear ProSafe. If you decide to go this route, don’t plug in that cable until you have removed PVID 1 from that port or you will cause a loop and bring your network down. Then I just logged into the ProSafe and set the QoS Rate Limit for port 8 to 15 Mb/s.
Secure the Airport Extreme Guest Network
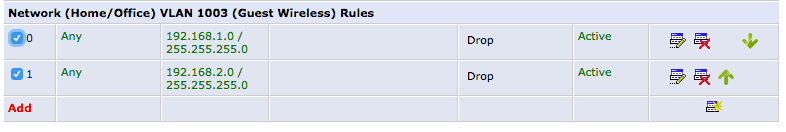
At this point all you’ve done is created another network, but they can all talk to each other. We don’t want the Airport Extreme Guest Network to be able to talk to our home network. Create a firewall rule that drops all packets from your main subnet to the guest network. On the ActionTech MI424WR this is accomplished by going to Firewall Settings–>Advanced Filtering–>The New VLAN you created–>Add.
I just entered the IP address ranges of my two existing VLANs, and set the action to Drop.
That’s it. Your new Airport Extreme Guest Network feature has been hacked to work on your 3rd party router! Users should be able to connect to the guest network, DHCP an address from the new IP range and access the Internet, but not your local private network!
So the answer is yes! You can use Apple’s Guest Wireless Network with 3rd party routers!!
This is super fantastico awesome to the extreme like made my day cool! Thanks!
Mike, this is a fantastic guide. Well written. I implemented same on a Sonicwall network with Netgear smart switches. Thanks for the inside info.
Any chance you’ve tested the exposure of the VLAN1003 guest network with an Airport Express? It would seem the firmware would be same (similar).
Thanks again!
You are a Genius! It worked perfectly!
I’m not a genius, but thanks for the kind compliments!
Well done, sir. I rarely leave kudos but here you went and provided a perfect solution to a situation for me and a client’s network. Thank you for taking the time to do this. Much appreciated. Ran right through it and voila. Good to go. I had to jump over 2 separate switches – coupled via fiber, etc. Hit the Sonicwall and created the fun. Some virtual networking on the Sonicwall was needed, and guest services was applied there as well to keep everyone from seeing one another on the guest wireless network, but it was all fairly straightforward. Thanks again.
So i have the same router connected to my ONT via the ethernet port and an airport extreme then plugged into port 4 of the actiontec router. I followed the instructions and it works but everything,regular wifi and lan ports included, connected to the extreme gets an IP address of 192.168.200.x. Shouldn’t you only get that IP range when connected to the guest network.
Yep. You did something wrong. Only your guests should get the .200 addresses.
Compliments for a well written post, and detailed advice. I also have two Airport Extremes in my house in bridge mode, while using a Synology router and managed switch in-between. I had wondered why the guest network on the apple extreme’s had not worked, and this answered the question. One rainy weekend I will try and implement your workaround. Cheers!
You may not need a managed switch; An unmanaged switch will typically pass through the VLAN-tagged traffic transparently. As long as you’ve got a matching VLAN interface tagged on your firewall uplink, you should be good to go. Tested with a Netgear unmanaged switch just to verify.
A lot of the Netgear devices are unmanaged “smart” switches, which will most definitely pass VLAN frames. Good call out! Thanks for the feedback!
Worked exactly as described! Thank you so much!!! And F*** Apple’s bullshit!
Hello , i would to set this up with a mikrotik router, im confused where u state if its plugged in directly to the router than go to next step, would that be just configuring another vlan on the router, also as of now i have one ethernet cable coming from the airport to the lan port on the mikrotik router.
Found this article via google search, and it helped me solve a related problem. My setup is a core router Apple Extreme, with two additional Apple Extreme’s in “Bridge Mode” and acting as wi-fi extensions attached to the LAN via Ethernet. In a three story house, one per floor equals great wi-fi all over. In the past I could never get the “Guest Network” feature to work. However after reading this article I had an epiphany, maybe the core switch is not passing the VLAN traffic. I tried plugging the secondary Airport Extreme directly to the core Apple router, and voila the guest network came alive! Therefore even with a complete Apple setup, you must deal with passing the VLAN traffic appropriately. I am sure I could have changed settings on the core switch to deal with it, but plugging it directly was an easy fix.
Very good instructions unfortunately my Centurylink modem does not offer such flexibility. With 8 airports extremes I have no other option than to use the CenturyLink modem with IPoE transparent bridging then the master AirPort Extreme in PPPoE then as the DHCP for the rest of my network and airports. Disappointing, I really wanted to control the guest bandwidth. Do I have any other options with my existing equipment?
Excellent info here. I have an Airport Extreme for WiFi on my network and the guest network stopped working once I put an ER-X between the APE and the modem. Using the info here, I was able to create a vlan for the ethernet port dedicated to the WiFi and separate the guest traffic to its own subnet. Vlan ID to 1003 and everything works great on the guest and main WiFi networks!
Thank you! 🙂
Thanks for this! My guest network stopped working on my AP Express ever since I started using pfSense. This solved my problem in a few minutes.
Thanks so much for your helpful article! Working like a champ on my Sophos UTM 9. Just had to create the VLAN and then assign it to the DNS, DHCP and Web filtering profiles as if it were another real interface. With your instructions it look just 3 minutes!
I’m about to try this with Sophos UTM too. Did you experience the DHCP issues described on the sophos community? https://community.sophos.com/products/unified-threat-management/f/management-networking-logging-and-reporting/15694/vlan-use-on-home-utm. “you cannot have DHCP running on the native vlan (physical interface). You need to use all tagged vlan’s.” Mike, is there a VLAN ID for the non guest traffic? Great article!
Awesome insight. All I needed was that VLAN number and I was off to the races. I now have gig internet and a guest network!
Will this work with a Time Capsule? When I turn on bridge mode, the Guest Network option is disabled
I am using the latest time capsule and I am not able to see the guest network option while in bridge mode. Do you know if Apple plugged the bridge mode bug in the time capsule?
I am trying to setup a vlan to the TC from my Ubiquity router.
Mike I just came across your write up. I appreciate this. Is there any alternative to achieve this with a router that doesn’t seem to have a VLAN setting? I am using a RAC2V1K router.
Gold! I’ve been running several of the AirPort Extreme units for a couple years. Wanted to create an isolated IoT network using the Guest function (while using my Cisco switch). Enabled the VLAN, tagged the ports and we’re in business. Thanks again!
Dear Mike, i’d like to setup my home situation as mentioned above. The one thing i don’t get is that the airport extreme only has one WAN port. So i only have one port to connect to my switch or router. That means i would have to enable two LAN / DHCP settings to this one port, one with a VLAN tag of 1003. Wouldn’t this create a conflict on my network? Or did i miss something?
Thanks in advance for your time and effort.
VLANs operate on the same port. That’s the whole point of them.
Thanks for your reply. I’m no expert in using VLANs. So if i setup my router with 2 LANS / VLANS , one with a DHCP scope for my internal LAN and one with a DHCP scope for my guest network (different range offcourse with a VLAN tag 1003) and i set them both up on port 1 on my router. Next i connect port 1 on my router to the WAN port on my Airport.
Would this mean that LAN/VLAN 1 without a VLAN tag would be used on the Airport for the lan ports and the primary Wifi network is setup and LAN/VLAN 2 with a VLAN tag of 1003 would automatically be used for the guest network i setup on the Airport extreme.
Thanks!
Exactly correct.
You’re the man!! Thanks for the support
Thanks for this, just saved my skin after I replaced an Airport Extreme router with an IPFire installation. As someone mentioned before me, simple unmanaged switches seem to have no problem passing the VLAN frames and my guest network is working very well.
Awesome! As for the switches it just depends. Newer “dumb” switches seem to work. Older “dumb” switches will drop the frame because it considers it to be corrupted.
However, be aware that this MAY give the guest layer 2 network access to your home network depending on how the switch is actually handling it. And if that happens a hacker could easily sniff your private network traffic.
Hi Mike, I stumbled on your blog while looking for a solution to a requirement for a second network. I use 4th & 5th gen Airport Extremes for my WiFi and this looks exactly like what I need. But it looks like Apple has done “it” to me again.
I am using Airport Utility 5.6.1 with Airport Extreme firmware 7.6.4 and the only way I can get the guest network tab to display is to switch connection sharing to “Share a public IP address” on the Airport. I can then switch to share mode and enable a guest network. But, when I switch back to bridge mode, the utility pops up a Connection Sharing error that says “Guest network requires that the Airport Extreme be set to share a public IP Address using NAT/DHCP.”
Is there any way you know to work around this?
Please disregard. I gave up and posted the question too soon.
I normally use the Windows version of Airport Utility which is installed on a domain controller. Switching to the iPad version allows the guest network while in bridge mode.
4
My router won’t support VLAN’s, my switch is manageable. Can I get my guest wifi network to work?
Hello Mike, A very good write up. I would like to know if it is possible to assign the TC’s address under default Vlan network and pass 2 more Vlan’s one (any vlan id other than default 1) for the main network and one for guest (which would be 1003). Any feedback is much appreciated. Thanks.
I’m not really sure I understand your question. But the TC does not allow any configuration of VLAN IDs.
My question is, can I choose what network subnet should be used as “Main” network on TC
Default/Management with VLAN id 1 (an IP from this range of network addresses is assigned as TC’s IP) Untagged
Private/Main Network with VLAN ID 10 (a different subnet from default / Management VLAN ID) – Taggged, which I want the TC to issue to the devices connected to it.
Guest Network with VLAN ID 1003 -Tagged which would be for guests.
Thanks
Barath
Not that I know of. You can’t configure the VLANs at all on these guys. You could do that on your switch with VLAN mapping though (VLAN translation) if its got that feature.
5
I implemented with several Airport Express devices and it worked.
Mike, thanks for the great article. It worked well for my home network, with several Airport Express devices in bridge mode, a Netgear switch, and the FIOS router. Interestingly, it seems the router won’t VLAN 1003 devices to to see VLAN 1 devices. I didn’t have to install the filtering rule you recommended. Not sure why.
Hey great article — honestly its too bad that the Airport Extreme doesn’t allow tagging or setting of the VLID on any of it’s ethernet ports. It’s great its able to have a wireless network with VLAN tag 1003, however it would be also great if they extended the ability to tag individual ethernet ports or at least set the default VLAN for each prot
Time capsule has exactly the same issues and I believe this solution should do the trick
Thanks a lot for this article. I managed to set my guest wifi with my cisco switch and forti router.
Great info from you and did the trick.
Hi I really appreciate this information. I’m trying to put a Time Capsule onto the same actiontec router you have and make a guest network. I’m trying to put all my kids devices on a firewalled network. I got all the way through your tutorial but when you said go to the actiontec firewall settings/advanced filter/select new VLAN/”ADD” I have different TWO options. There is IN with list of networks, and out with list of networks. My advanced filter options (for both in the IN and the OUT) include “source address, destination address, protocol” with drop down menus. Then there are three items with boxes to click: DSCP, Priority, Length. I don’t see anything about IP address range. I understand what you did but my menus look different. Sorry I’m late to the game I set up the guest network years ago and we never used it because kids weren’t old enough.
1
Very useful. Came as the first search result in Google and VLAN ID was what I was looking for. Thanks.
Mike, Just a short note to say this is still a very useful post.
I have set this up using Verizon Fios Gigabit internet and a Ubiquiti Dream Machine as my router, networking to 8 Apple Airport Extremes. [Yes it is a large house with lots of brick walls]
I got most of the Airports second hand on e-bay as I don’t want to do a full upgrade until WiFi 6E is widespread and affordable. The Airports are providing between 400 Mbps to 590 Mbps depending on the location. Speed may be limited by the devices connecting but this is more than enough for my needs.
Being able to set up the Guest network was a real benefit, particularly as I can put all my IoT devices on the Guest network and keep them [and their no doubt many insecurities] away from my main network.
Thanks very much